Political revolutions have a tendency to backfire. The high ideals of “liberty, fraternity and equality” behind the 1789 French Revolution ended with the guillotine. In the Russian Revolution of 1917 the promises of “peace, bread, and land” led to the Gulag. Even technological revolutions of the past had have downsides to them. One possible cause for failed revolutions is a poor appreciation for the challenges in implementing the promises. It is just not that easy to put some Revolutionary new idea into practice without the necessary awareness of the dangers ahead and of the precautions that must be taken to insure successful implementation. There seems to be a similar tendency in some of the so called revolutions taking place in high technology today. I have noticed a lack of awareness of the security implications when new Information and Communications technologies (ICT) are introduced at ICT themed conferences over the past years. This has a serious implication for the decision maker attending these conferences who may get an inaccurate picture of what is happening in cyberspace. The result may be poor security policy that leaves out a necessary mitigation strategy to deal with an important threat such as a state sponsored cyber-attack targeting the new product or service. I still remember attending the U.N.’s Internet Governance Forum in Vilnius in September 2010. One of the main themes of this gathering of ICT policy professionals was insuring Internet access for all (1) . Listened to many presentations and was puzzled why security was hardly ever mentioned. I raised my hand and pointed out that since the last Forum meeting a country was forced by a DDOS attack to disconnect itself from the Internet (Estonia in 2007). In addition a cyber-attack was used for the first time in a military operation which contributed to another nation being cut off (Russia-Georgia War 2008). It may not have had time to sink in by then but information about a state sponsored cyber-attack against a control system (Stuxnet) was certainly in the ICT practitioner domain. I said that certainly these examples merit serious attention for they do concern the main themes of the Forum and in some cases represent cyberspace misbehavior by some of the U.N. member states being represented. I was politely thanked by the plenary chairman and then the next questioner was recognized and that was it as far as discussing cybersecurity.
Something similar happened at an ICT conference sponsored by another international organization, the European Union, which was held in Vilnius in 2013. There the main theme was characterized by the words “Create, Connect, and Grow” using the “fruits” from the new applications of ICT (2) . The logo for this conference featured a biblical like image of a tree with the fruits (some low hanging) of technology just waiting to be picked. No reference was made to any hi-tech “forbidden fruit” on that tree nor was any cyber “serpent” visible in the image that represented the negative aspects of these technologies. By November 2013 there were additional reports about cyber incidents which also failed to find a place on the topic list of discussions (3) . In that year the notorious Spamhouse denial of service attacks on the Internet had threatened the functioning of the Internet (4) . Issues of privacy, surveillance, and Government cyber power used against citizens and other Governments raised by Mr. Snowden’s revelations also did not seem to make an impression at this conference(5).

(Would be a better conference poster if the word “SAFELY” was added after the word grow.)
Photo by V. Butrimas
Even industrial sector specific conferences that I attended also were not getting it in terms of a realistic awareness of cyberspace threats to the technologies and products being promoted. Once again I did not have to travel far to participate in the “Innovative Energy Solutions for Military Applications” (IESMA 2014) IESMA (6) conference. Amidst a euphoric atmosphere on energy innovation for the military, security again was not being mentioned. I raised my hand and asked why. One of the explanations was that “security is a separate topic” that does not come under the remit for this conference. Took a walk to the exhibition floor and visited the booths of control system manufactures (there were some big names in the industry represented). I asked a few vendors why their product brochures had no mention of security. Have they heard of the vulnerabilities being discovered in control systems? Yes, a portable military base power system is a good idea but has the risk of using Bluetooth and Wi-Fi connectivity been evaluated against the risk to soldiers using this equipment in a hostile environment? Have they heard of STUXNET? One vendor told me he was sure the safety aspects were considered and promised to get back to me after he had consulted with his engineers. The salesman also asked “and by the way how do you spell STUXNET”? These are just a few examples of real conversations I had at these conferences.
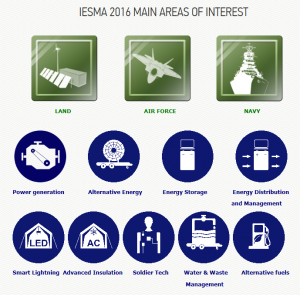
(Security concerns perhaps are implied in the listed areas of interest above but deserve a separate listing.)
Today one of the new technologies being promoted in the critical infrastructure sector is the “Smart Grid”. It has been described as a “revolution” in terms of providing new rights to electric customers. It is being sold like most new tech products in this sector as a technology that offers new possibilities for consumers, operators and for conserving energy. However the movement to sell and implement this technology seldom mentions concern for dealing with the new vulnerabilities that tend to be introduced in tandem with the new equipment. For example in a recent BBC NEWS article a high U.K. Government official responsible for the electric grid appeared to claim that this new technology will insure against blackouts. Blackouts that can be avoided by taking advantage of the flexibility in power distribution the smart grid will provide (7). However the use of fanciful terms like “internet of energy” in the article gives reason to pause and wonder about the officials’ understanding of smart grid technology and its security implications.
I mentioned in an earlier blog about a conference of electrical industry representatives and engineers where smart grid technology was also promoted (8). Missing again was a sense of a clear understanding on the part of the Smart Grid proponents for the cybersecurity risks involved in the remote monitoring and management of smart grid devices. Very impressive and useful capabilities but very dangerous if the accompanying vulnerabilities are not recognized and addressed. The Ukraine blackout of last December is an example of the malicious turning of the technology tables against the operator of a power grid. The journalist and national electric grid official in the BBC interview seem totally unaware of the malicious aspects of a hostile actor taking over control of the substation switches by remote control, installing malware on communication devices and then erasing operator workstations as happened in Ukraine. Is there a euphoric smart grid parade underway that remains unaware of the dangers that need to be addressed?
It appears that there is a potential danger for a dangerous disconnect between the design of new systems like the smart grid and security. They both need to be included in the same discussions right from the beginning of the design phase and certainly well before the marketing phase. Otherwise expectations will be raised by industry on a technology that may not be as safe as it could be. A while back a U.K. University published findings from their study of the cybersecurity of automated traffic light systems. They did find security flaws in the wireless communications between devices which could be maliciously manipulated. The findings were presented to the manufacturer which responded by saying that their products were designed according to all the standards concerning traffic lights but that the standards did not include security (9). How widespread is this kind of blinkered security mindset among designers and manufacturers that are now with enthusiasm putting these new high tech devices on the market? One can understand the pressure for a manufacturer to put out a product ASAP in order to get some return on investment. However, technologies like the smart grid if implemented extensively will affect the lives of many people in serious ways if something were to go wrong. Will manufacturers fix the flaws when they are reported in a timely and customer friendly manner? I would hate to hear about the IT tradition of “Patch Tuesday” and other after-the-fact fixes which we have come to tolerate in the world of Windows software being carried over to the world of control systems or IoT. The stakes behind such fixes are much higher and have larger implications for the well-being of society.
1 http://www.intgovforum.org/cms/component/content/article/96-vilnius-2010-meeting-events/475-preparing-the-igf-2010-meeting-
2 https://ec.europa.eu/digital-single-market/ict-2013
3 http://mspmentor.net/managed-security-services/opendns-research-top-5-cyber-attacks-2013
4 http://www.itbusinessedge.com/slideshows/the-most-significant-cyber-attacks-of-2013-04.html
5 https://ec.europa.eu/digital-single-market/en/ict-2013-conference
6 https://nato.mfa.lt/nato/en/news/registration-to-iesma-2014-conference-extended
7 http://www.bbc.com/news/business-37220703 31 August 2016
8 http://scadamag.infracritical.com/index.php/2016/08/03/smart-technology-that-isnt-so-smart/
9 https://jhalderm.com/pub/papers/traffic-woot14.pdf (see page 8)
